Instantaneous attack
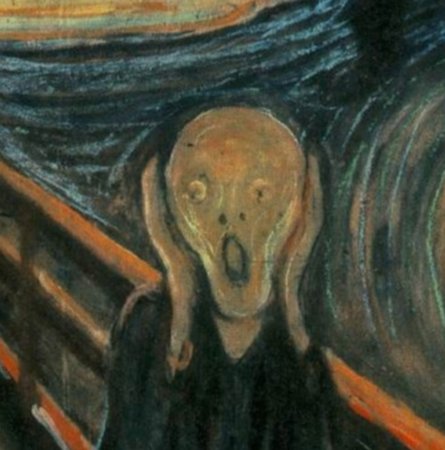
While building up a new Linux machine and installing LinBPQ, I decided to open up the telnet port on my DMZ router so a friend could access the BPQ ports. Within mere seconds an IP address beginning with 222 commenced an attack on the port. Yes seconds, not minutes, not later that afternoon, but about 15 seconds. I made a quick test from an outside machine to confirm it worked, it did, and shut down the NAT. Peace returned and all is well.
222.x.x.x
Anyone with a basic understanding of Internet security will know the above IP first octet likely belongs to our friends in Asia. It goes without saying you have to weigh the good and the bad for some portions of the Internet. Blocking access for a public website is one thing, but for something like this BPQ machine, blocking it all makes sense.
Thoughts about mixing packet with Internet
Packet node software is written by volunteers with the best of intentions. However, one must be wary of the security awareness of the authors. Their focus is likely on proper operation of software, not necessarily the security thereof. Indeed many software authors may expect the user to provide an operating system based security blanket around their code. A layered approach towards internet security is not without precedent as OS solutions are likely to be a more practical layer for blocking nefarious intruders.
From day one, the design of VAPN includes no, zero, nadda Internet connection of any kind whatsoever. Occasionally I listen to the pleas of Winlink users and think about including this service as part of the VAPN tool list. Then events like above occur and remind me of just how dangerous the real Internet is to the VAPN gear, other Winlink systems, and, for that matter, telnet to telnet message passing over TCP/IP. Hence, if VAPN ever has a connection to the real Internet for any purpose, a whole lot of thinking will go into security. That takes time. VAPN will roll out standalone first… and maybe forever.
Telwhat?
Imagine during the holiday season you strike up a conversation with a relative or friend in the Internet security field. Seeking sound advice you make it known amateur radio packet systems communicate with each other over the Internet via telnet ports using usernames and passwords. Might the reaction be:
- A long blank stare of horror?
- Uproarious laughter since telnet hasn’t been taken seriously for 20 years?
- “You mean you’re not using SSH port tunneling or a VPN?”
- Combination of the above.
If we cannot understand the fearful reaction IT pros might have about packet systems’ communication modes of Internet antiquity, don’t be surprised to not be taken seriously.
Conclusion
Stopgap, protempore, Internet independent messaging systems need to work if the Internet goes south.
The Internet has made security advancements to combat the uptick in attacks. OTOH packet systems with Internet exposure really haven’t. That’s okay so long as you don’t mix the two.